A thief picks a lock to open it. But if the key is already available, it’s a piece of cake for the thief. Such is the nature of applications and hackers today. All it takes is one mistake from the developer(the key) and the hackers capitalize on that mistake (the theft). It has been rightly said, ”Security is only as strong as the weakest link!”
It won’t be an exaggeration in stating that there are an infinite number of applications present today on the internet. The applications present on the Internet can be classified into the following categories :-
- E-commerce applications
- Healthcare applications
- Financial/Banking applications
- Other generic applications
Many of these applications deal with sensitive customer data categorized as Personally Identifiable Information(PII) and Protected Health Information(PHI). These sets of data can be exploited if they fall into the wrong hands. The data we put on the internet is not safe unless the application that handles our data is secure enough.
When it comes to mobile applications, we all know how popular they have become. The increase in the no. of mobile applications and their users is remarkable. An insight from comSCORE(shown below) further proves this point :-
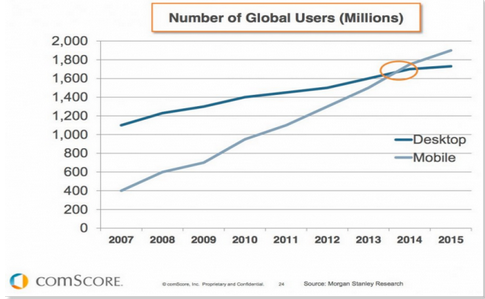
This fact draws the interest of crackers(hackers with bad intentions, real bad!) towards mobile applications. The number of target victims automatically increases if a mobile application is compromised. Simply stated, mobile applications are under equal risk as the web applications.
Common mistakes that may put your web and mobile application under risk are :-
- Improper input filtering – You just cannot trust user input. Most of the applications are compromised because they do not pay proper attention to the input they allow from the user. Some of the major vulnerabilities that result from improper input filtering include Sql Injection, Cross Site Scripting and Unrestricted File Upload.
- System Misconfiguration – It is not only required to write secure code but also how securely it has been implemented. However secure the application maybe, it is as vulnerable as the vulnerable server that it has been implemented upon. This may lead to vulnerabilities like Insecure Console Access, Service level DOS, Server Privilege Escalation, Transport Layer Attacks and Improper File Permissions.
- Authorization Bypass and Privilege issues – I have a resource in my application. It is private to me. I don’t intend to share it with anyone. But i make a mistake. Turns out, it can be easily referenced by just making a small change in the URL www.example.com/id=user1 . I was depending on the fact that no one would try the URL www.example.com/id=admin. Now, i am hacked. Sounds too simple? Maybe it does, but these mistakes are very common and result in authorization bypass. If you take responsibility of user’s data, you are also responsible for its security from such attacks.
- Information leakage – Sometimes when you try to access a particular resource and it doesn’t exist, you get an error. Typically, Error 404 Not found. But what happens when the application returns an error stack trace instead? You are able to view the source code! This type of information leakage can be dangerous if a certain snippet of code leaks how the application works or database related details or server details, and in worst case some critical application data.
- Insecure APIs – A web service communicating with another web service sounds like a great idea. This model has simplified the tasks of the developers. Every developer wants to create such APIs that ease his work and provide better results. But not everyone follows the best practices while writing APIs. There have been many cases where an insecure API was responsible for an application getting compromised.
- Lack of Encryption – The data you collect from the user should be encrypted before being stored. There are still many applications that store user password in clear text. As per the best practices, data at rest and data in transit both should be encrypted in a proper way, otherwise it may lead to attacks like man in the middle attack.
Companies have incurred huge amount of losses due to these mistakes. The losses have been in form of Monetary Loss, market value, defacement affecting the image of the company and loss of customer’s trust. “According to IBM, the average per capita cost of data breach was $217 in the US and the average total cost of data breach was $3.79 million due to security breaches in 2014.”
Is it too late to act? Well, no. Whether you have been hacked or not, it’s never too late to take security measures. You may have heard, “The best defense is a good offense.” So, hack yourself before the hackers do. You can use the assessment tool mentioned below to judge how secure is your application.