Logs Monitoring Using AWS CloudWatch
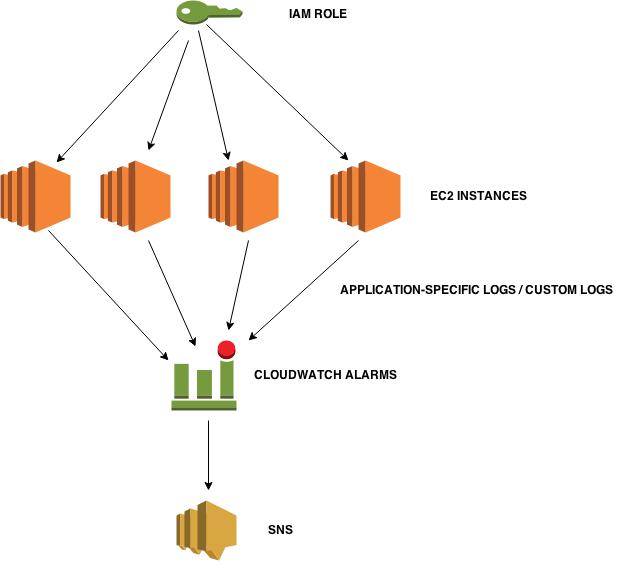
Suppose, you have multiple servers running a simple web application on apache or Nginx and you want to put all the error/access logs on a centralized place so that you can troubleshoot your system in case of any error after getting alert notification configured on your logs .
Here is an amazing feature of Amazon Web Services Cloud Suite by which you can achieve this task.
Amazon CloudWatch now provides us the flexibility to monitor, maintain, store and access our custom log files, log files from EC2 Servers, CloudTrail and other resources. We can also generate alerts on those logs. This will help us in troubleshooting our servers by monitoring all the appplication-specific logs on CloudWatch in real time.
Implementation:-
Step 1 :-
Firstly we need two policies attached to an IAM role which we will assign to EC2 instances so that the logs from the instances can be pushed to the CloudWatch.
There is a need of an CloudWatch agent which will do the task to push logs onto the CloudWatch.An agent-configuration file is necessary which we can store in our S3 bucket and at the time of launching an instance we will use that agent-configuration file.
The two necessary policies are :-
Policy 1 :-
This policy will allow your EC2 instance to access the agent-configuration file stored in your S3 bucket.Here you would give the name of your S3 bucket.
{
“Version”:”2012-10-17″,
“Statement”:[
{
“Effect”:”Allow”,
“Action”:[
“logs:*”,
“s3:GetObject”
],
“Resource”:[
“arn:aws:logs:*:*:*”,
“arn:aws:s3:::your_bucket_name/*”
]
}
]
}
Policy 2 :-
This policy will allow your EC2 instance to push the log file stored in your CloudWatch.So here I am assigning all the permissions to my EC2 instance so that it can create log group,log stream and other necessary files.
{
“Version”:”2012-10-17″,”Statement”:[
{
“Effect”:”Allow”,
“Action”:[
“logs:*”
],
“Resource”:[
“arn:aws:logs:*:*:*”
]
}
]
}
So create an IAM role and assign two policies to it and at the time of launching EC2 instance you will be assigning this role to your EC2 instance.
Step 2 :- Understanding Agent-Configuration File (stored on S3)
Now, create an agent configuration file Cloudwatch_agent_conf and paste the content of following file and edit it accordingly and upload it to your S3 bucket.
[general]
state_file = /var/awslogs/state/agent-state
[/var/log/syslog]
file = /var/log/nginx/access.log
log_group_name = nginx_server
log_stream_name = nginx_access_logs
datetime_format = %b %d %H:%M:%S
Parameters in agent-configuration file :-
1.file :- The file specifies the file in which your actual logs are stored on your EC2 instances. This is the log file whose content you want to push on CloudWatch logs . I want to push my nginx access logs onto the CloudWatch so I am specifiying the path of nginx access log file.
2.log_group_name :- It refers to the destination log group. A log group will be created automatically if no log group exists in your CloudWatch.
3.log_stream_name :- It refers to the destination log stream.A log stream can be {instance_id}, {hostname}, {ip_address} or a combination of these.
4.datetime_format :- It specifies how the timestamp is extracted from logs.
%b specifies month (Jan,Feb..)
%d specifies day of month (01,02..)
%H specifies Hour (24-hour clock)
%M specifies Minutes (01,02..59)
%S specifies Seconds (01,02..59)
Step 3 :- Now, we need a script which we can pass in the User data at the time of launching an EC2 instance which will make all the configurations for CloudWatch agent to push logs to the CloudWatch.
#!/bin/bash
wget https://s3.amazonaws.com/aws-cloudwatch/downloads/latest/awslogs-agent-setup.py
chmod +x ./awslogs-agent-setup.py
./awslogs-agent-setup.py -n -r us-east-1 -c s3://your_bucket_name/Cloudwatch_agent_conf
sudo service awslogs restart
Step 4 :- We are almost done with the configuration . Now, launch a new EC2 instance, assign it the IAM role with two policies which you have created above and pass the above script as a userdata to the instance.
You can also append other packages’ installation steps after these lines in userdata script like installation of nginx or apache.
Now go to your AWS CloudWatch console.Go to “Logs” in Dashboard, you will be able to see the log group name which you mentioned in your agent-configuration file.
SNS Integration on Logs to create alerts
Step 1 :- Go to the Log Groups in your AWS CloudWatch console .Click on Create Metric Filter.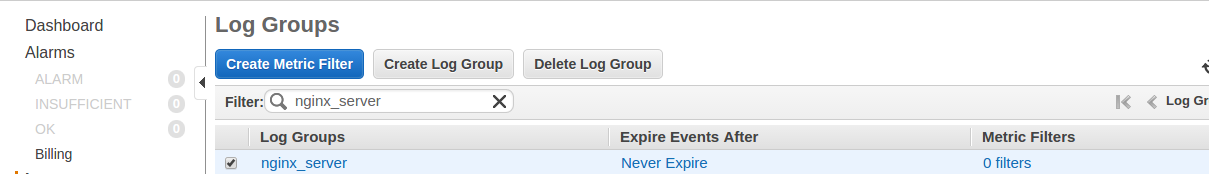
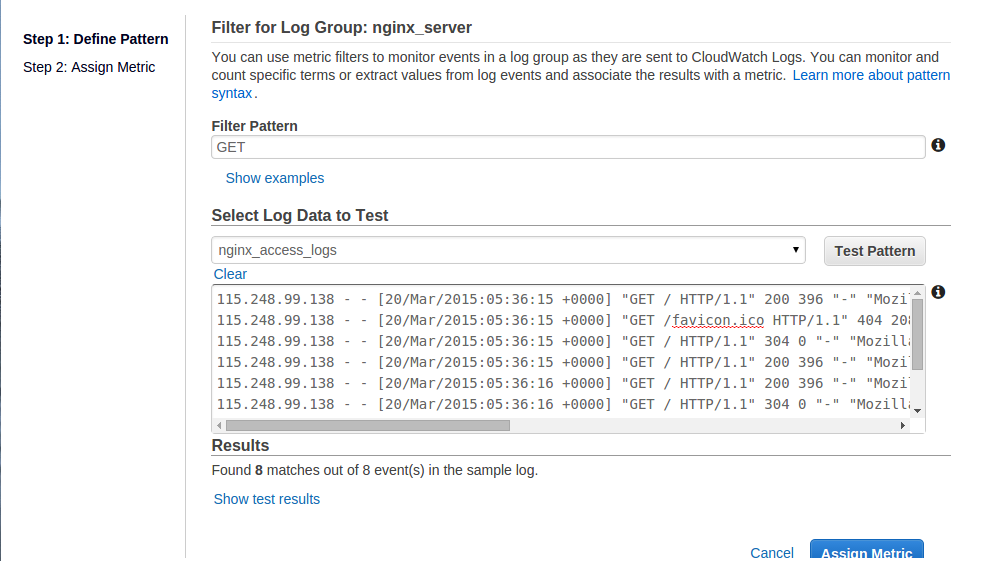
Step 2 :- Now, you can set pattern to be searched in logs.
For Example, I want to create alarm according to my GET requests.Click on Assign Metric.
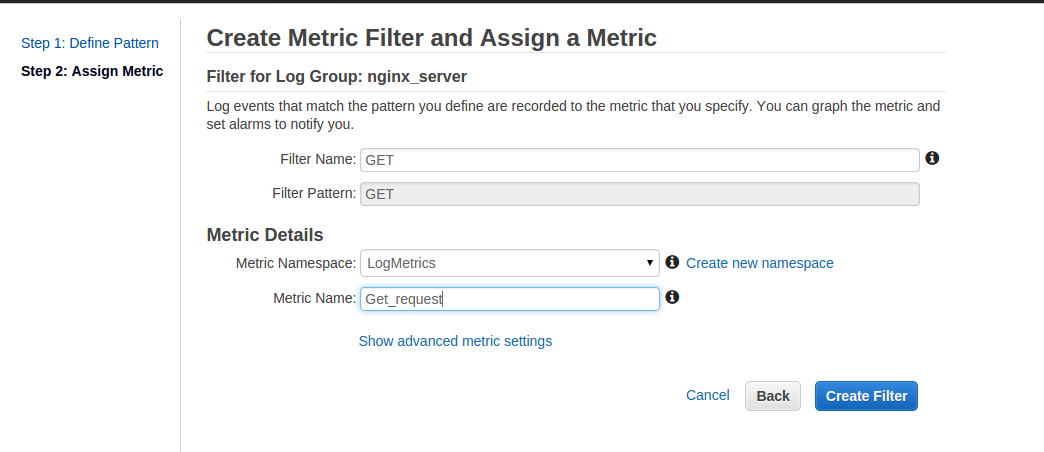
Step 3 :- Now, assign a metric to your metric filter.
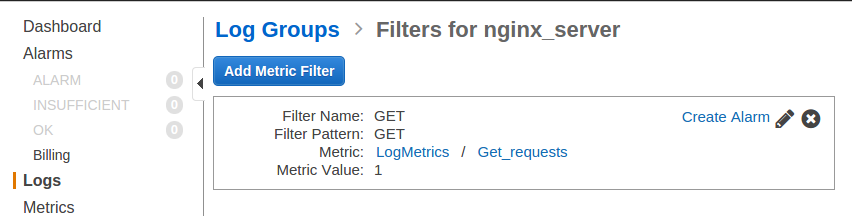
Step 4 :- Your metric filter is created.Now click on Create Alarm .
Step 5 :- Here you can create alarm by setting thresholds and ARN for your SNS.
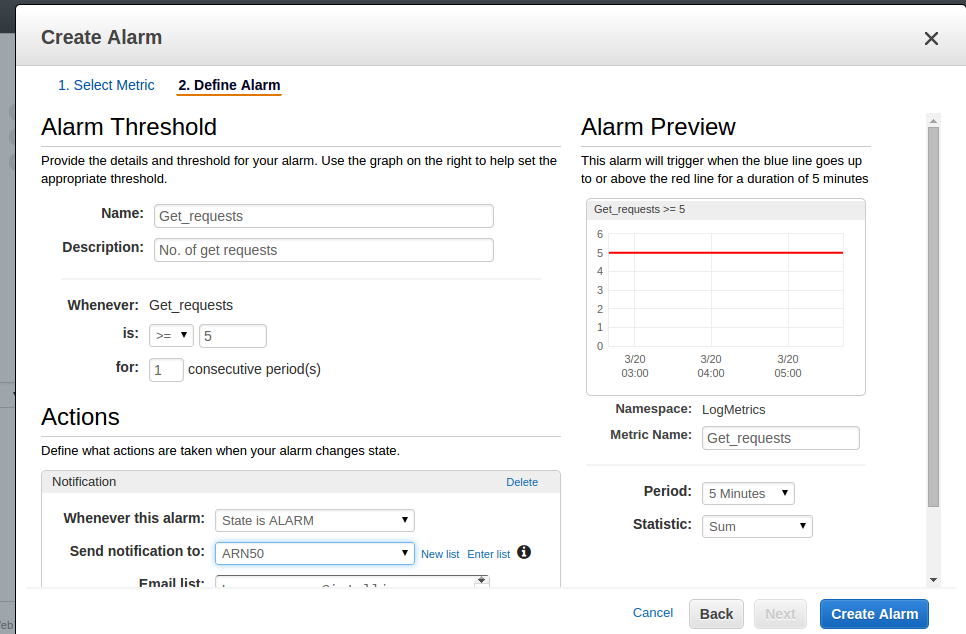
Finally your alarms are configured on your logs.You can check your alarms in CloudWatch alarms.




Nice article. Just to add to it. You can view alarms from multiple CloudWatch accounts on the same screen using third-party wrappers like SpectrumApp.io.