Streaming Videos On Demand using Amazon Cloudfront and S3
I came across a scenario where we have to stream Videos On Demand (VOD) using Amazon CloudFront and Amazon Simple Storage Service (S3). The on-demand streaming is done using Cloudfront Content Delivery Network (CDN). The videos to be served are stored on Amazon S3. I have designed a secure architecture for the same setup.
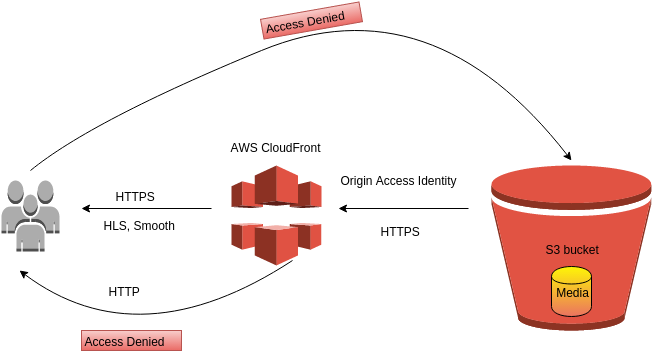
- The user sends the request to AWS CloudFront CDN for the video to be streamed.
- The request is preferred to be sent on the HTTPS protocol. For more secure streaming, all requests being made through HTTP protocol are denied by the CloudFront.
- The videos to be served are stored on AWS S3. The CORS configuration is set so as to allow access from the desired domains only.
- The access to S3 bucket is made through HTTPS protocol for more secure architecture. The HTTP requests are denied by AWS S3 policy which will be described later in the blog.
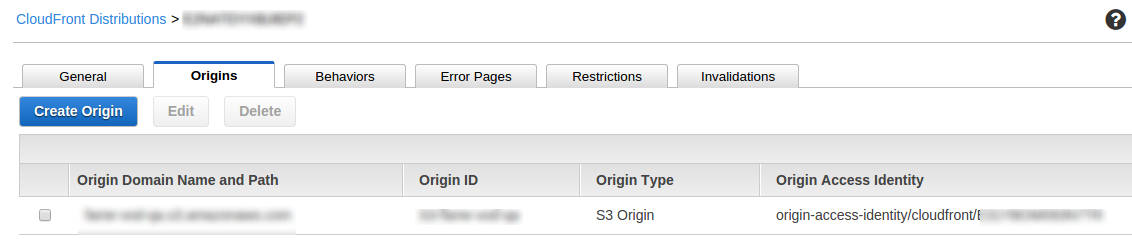
- The CloudFront Origin Access Identity, which is a special Cloudfront user is used to restrict access to the content in S3 buckets. The access is given only through the CloudFront so that the users cannot access the content directly by using S3 url.
Creating Amazon S3 bucket to store video content
The following steps are performed to create Amazon S3 bucket and modify its permissions:
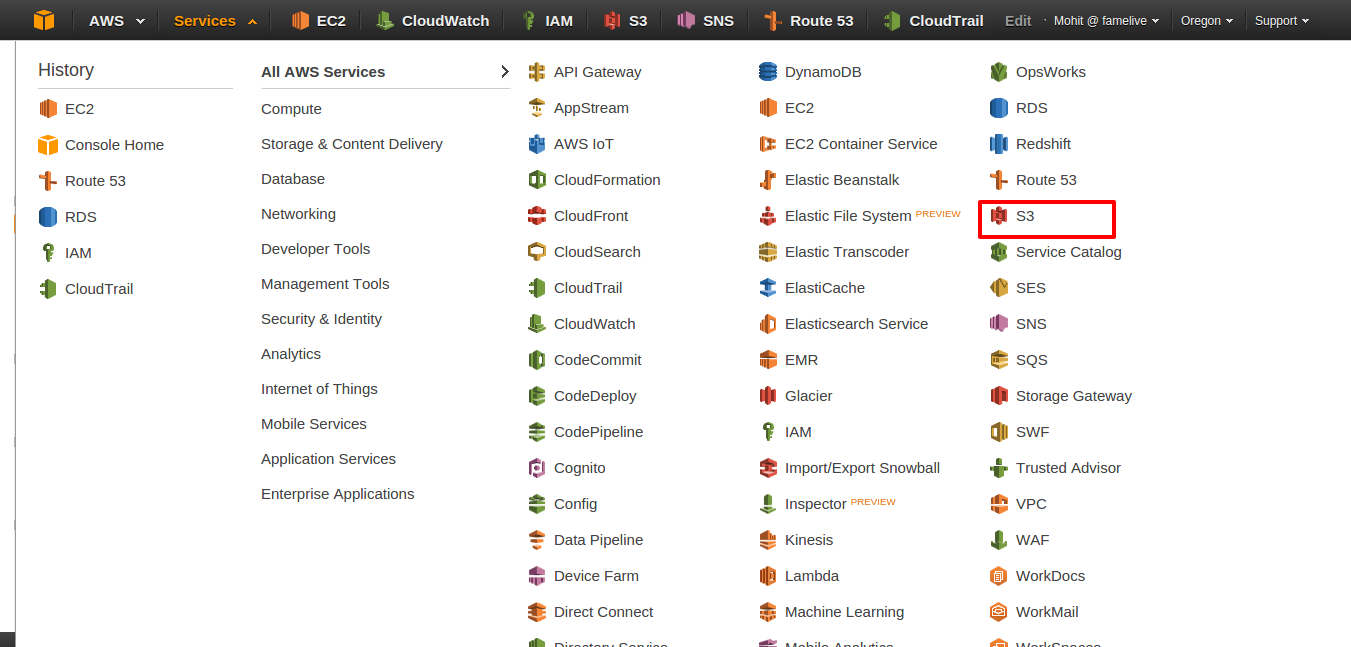
1. Go to S3 console by logging into AWS console. Click on S3 option as shown below:
2. Create a new S3 bucket by clicking on Create Bucket button. Specify the name and region of the bucket.
3. Upload the video files to be served on the bucket by using AWS console or AWS CLI.
4. Create a file named crossdomain.xml and upload it. The file should contain the following content:
[js]
<cross-domain-policy>
<allow-access-from domain="*" secure="false"/>
<site-control permitted-cross-domain-policies="all"/>
</cross-domain-policy>
[/js]
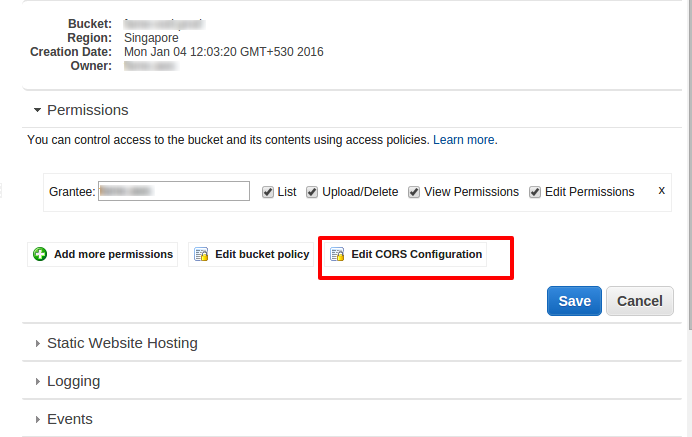
5. Update CORS information by clicking on Edit CORS configuration as shown:
6. Put the following content in the CORS configuration file:
[js]
<?xml version="1.0" encoding="UTF-8"?>
<CORSConfiguration xmlns="http://s3.amazonaws.com/doc/2006-03-01/">
<CORSRule>
<AllowedOrigin>*</AllowedOrigin>
<AllowedMethod>PUT</AllowedMethod>
<AllowedMethod>POST</AllowedMethod>
<AllowedMethod>DELETE</AllowedMethod>
<AllowedMethod>GET</AllowedMethod>
<ExposeHeader>ETag</ExposeHeader>
<AllowedHeader>*</AllowedHeader>
</CORSRule>
</CORSConfiguration>
[/js]
Here AllowedOrigin tag ensures the host from which the access to the content is allowed. You can set it to your desired host. AllowedMethod tag ensures methods allowed on the bucket.
7. Now update the S3 bucket policy by clicking on Add Bucket Policy near Edit CORS configuration option. The policy must contain the following content:
[js]
{
"Version": "2008-10-17",
"Id": "some_policy",
"Statement": [
{
"Sid": "AddPerm",
"Effect": "Deny",
"Principal": "*",
"Action": "s3:*",
"Resource": "arn:aws:s3:::<strong>bucket_name</strong>/*",
"Condition": {
"Bool": {
"aws:SecureTransport": false
}
}
},
{
"Sid": "2",
"Effect": "Allow",
"Principal": {
"AWS": "arn:aws:iam::cloudfront:user/CloudFront Origin Access Identity <strong><strong>OriginAccessIdentityID</strong></strong>"
},
"Action": "s3:GetObject",
"Resource": "arn:aws:s3:::<strong><strong>bucket_name</strong></strong>/*"
}
]
}
[/js]
The bucket_name should be replaced by the name of the bucket and OriginAccessIdentityID should be replaced by CloudFront Origin Access Identity. It will be obtained when we create the CloudFront distribution below.
Here “Effect”:”Deny” aws:SecureTransport”: false is used to prevent HTTP access to S3 bucket. The GetObject permission is given of the content in S3 only to the cloud front user.
Creating Amazon CloudFront distribution to stream video content
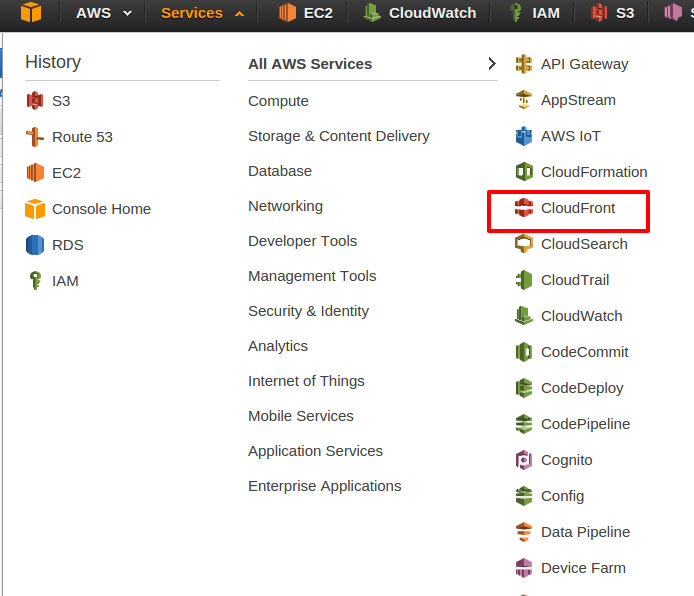
1. Go to CloudFront console by logging into AWS console. Click on CloudFront option as shown below:
2. Click then on Create Distribution to create a new cloud front distribution. The new distribution will be used to stream videos.
3. Click on Create Web Distribution.
4. Now enter the required details in the boxes as shown in the image below:
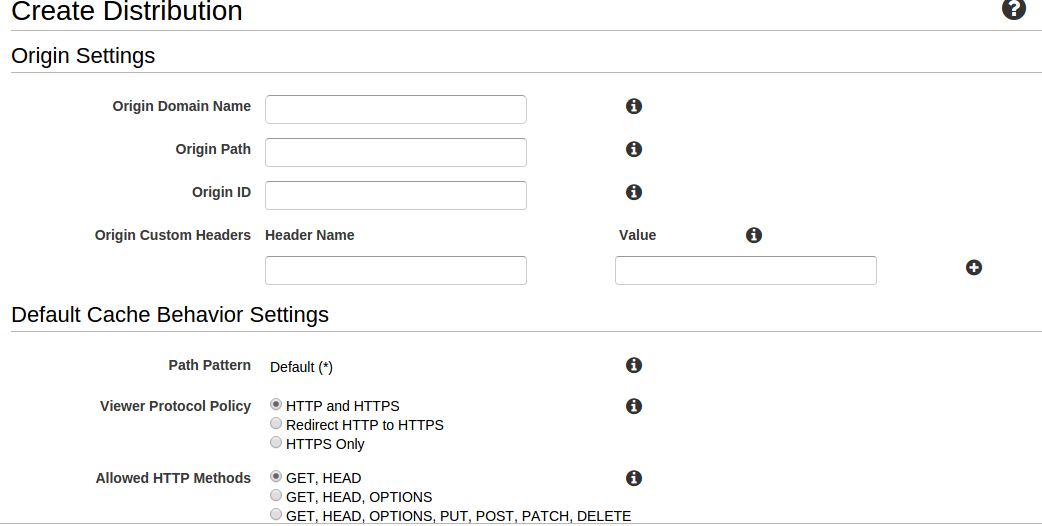
Origin is where you store your content to be served.
- Origin Domain Name: Choose Amazon S3 bucket you created above.
- Origin Path: Leave it blank.
- Origin ID: It will be automatically set on choosing bucket in Origin Domain Name above.
- Restrict Bucket Access: Choose Yes.
- Origin Access Identity: Choose to create a new Identity.
- Viewer Protocol Policy: Choose HTTPS only.
- Allowed HTTP methods: Choose the methods you want to allow.
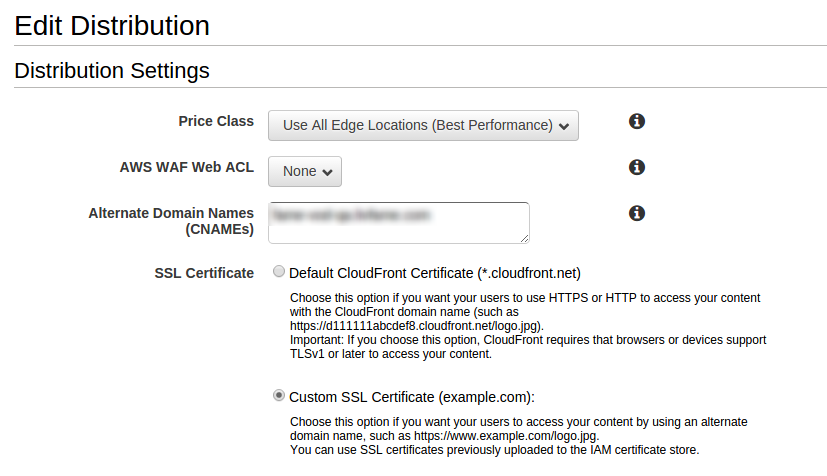
5. SSL Certificate: You can use default CloudFront certificate or can create your own certificate. To create your own certificate, follow the below steps:
- We need a server certificate, a private key and a certificate chain to create our own SSL certificate.
- Then using AWS CLI create certificate by:
[js]
aws iam upload-server-certificate –server-certificate-name YOURNAME –certificate-body file://YOURSIGNEDCERT.pem –private-key file://YOURPRIVATEKEY.pem –certificate-chain file://INTERMEDIATECERT.pem –path /cloudfront/path/
[/js]
YOURNAME – Identifying the certificate once it is uploaded to AWS console.
YOURSIGNEDCERT – The certificate received from Certificate Authority(CA).
YOURPRIVATEKEY – The private key, which is generated as a part of certificate process.
INTERMEDIATECERT – The intermediate key provided by CA.
The certificate will then be available on your AWS console. The certificate generated above can be verified by:
[js]
aws iam get-server-certificate –server-certificate-name YOURNAME
[/js]
Leave other options as default and click on Create Distribution.
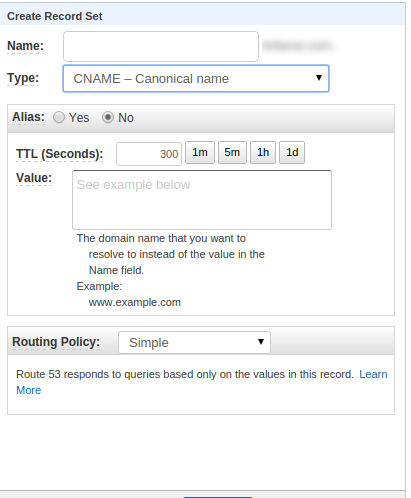
6. On Web distribution page, you will get DNS of your CloudFront as **************.net. Copy this and create a Cname in Route 53 as shown:
7. Now update this DNS in CloudFront distribution. Go to your web distribution. Click on General and then click on Edit. Then update DNS as shown:
8. The origin access identity will be obtained after you create the cloud front distribution. After creating the distribution, edit the distribution and origin access identity will be seen as below:
The CloudFront distribution will take some time to create. You can check the status at main distribution page. After the distribution is created, you can check out the complete secure architecture. The few testing steps are as follows:
- The content present on S3 will not directly be accessible by using the S3 url.
- Access the content by https://<cloudfront_dns>/<folder_name>/<file_name>.
- The content should not be accessible by http://<cloudfront_dns>/<folder_name>/<file_name>.
The secure architecture has been implemented. The architecture can be modified at ease by modifying the parameters or policies.




its giving me 403 error even after follow these steps properly please help ! !
very good block nice .
This blog is awesome. Kudos and a big thanks to the person who have written it.
Amazing blog. Thanks for sharing this 🙂
My pleasure 🙂