In one of my recent projects, while working on Jenkins, I was required to create and implement a Project-based Matrix Authorization Strategy.
Installation of Jenkins is a simple task, but it took me a while to implement this strategy and later I found it quite easy enough and thought of writing a blog.
Project-based Matrix Authorization Strategy is an authorization method using which we can define which user or group can do what actions on which job. This gives us a fine-grained control over user/group permissions per project.
We are starting with a fresh Jenkins installation. Jenkins could be installed using the following commands:
[js]wget -q -O – https://jenkins-ci.org/debian/jenkins-ci.org.key | sudo apt-key add –
sudo sh -c ‘echo deb http://pkg.jenkins-ci.org/debian binary/ > /etc/apt/sources.list.d/jenkins.list’
sudo apt-get update
sudo apt-get install jenkins
[/js]
Jenkins uses 8080 port by default so it could be accessible browsing below link
http://:8080
We would be welcomed by this page:
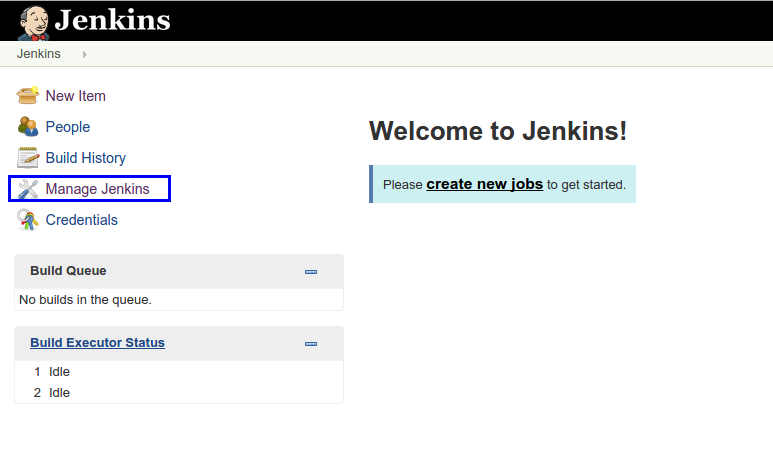
Now , click on “Manage Jenkins”, we would be navigated to the following page:
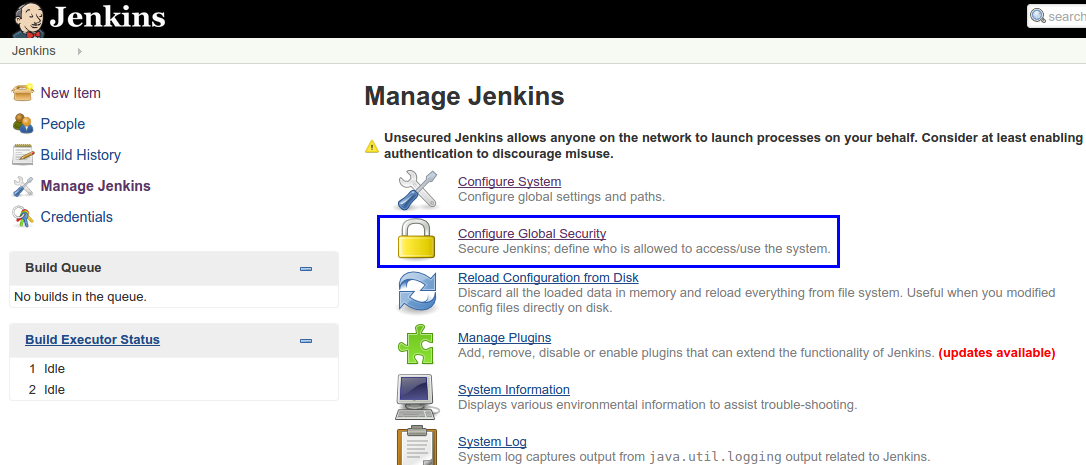
Click on “Configure Global Security” to move to Global Security page:
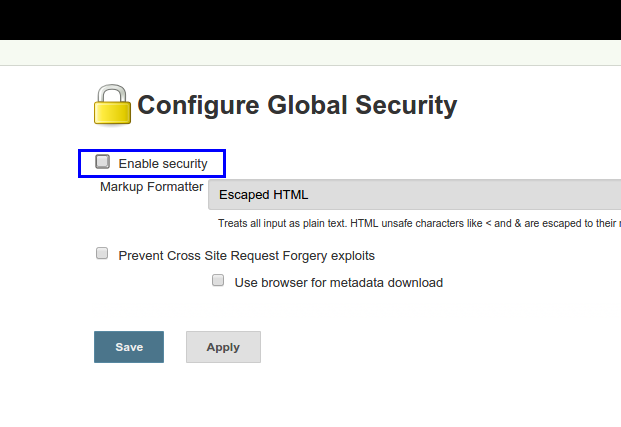
Check Enable security and more options would appear as shown below:
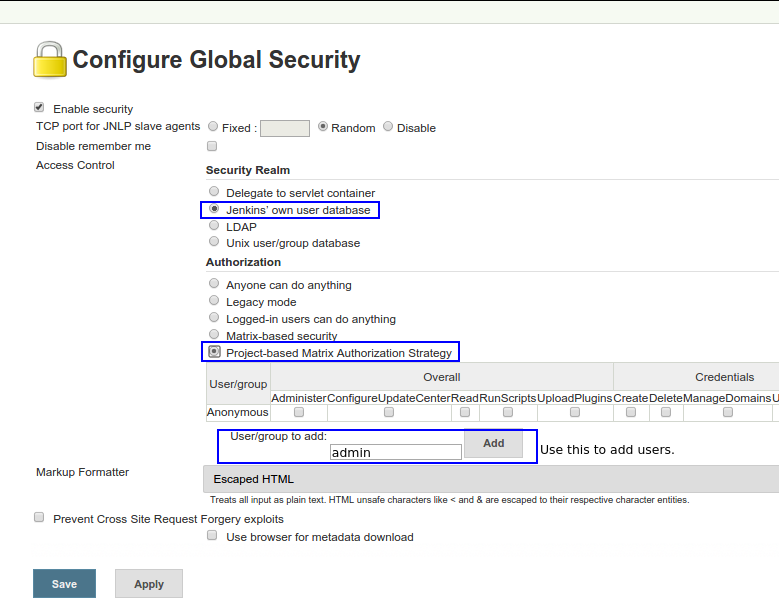
As we are creating new users in Jenkins, we would be using “Jenkins’ own user database”. Select this radio button under “Security Realm”.
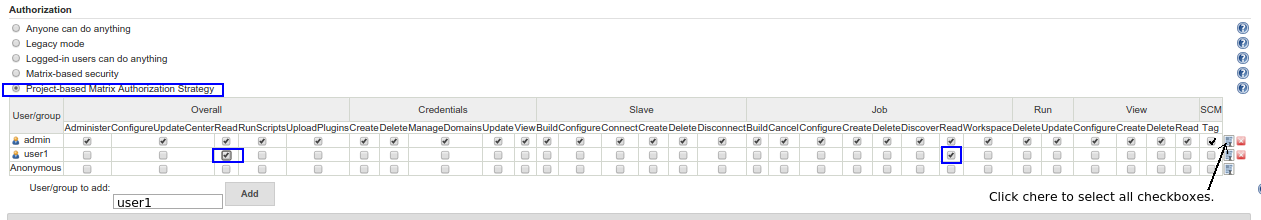
Under Authorization, select “Project-based Matrix Authorization Strategy” and add two users, one administrator (say admin) and a regular user (say user1).
All the checkboxes present besides users are for setting global permissions. Select all checkboxes against admin user to give admin full permissions.
For user1, we are selecting read permissions under jobs. With this, user1 would now have read permission to view all jobs which we would be creating later on.
We have to provide read permission under “Overall” category to any regular user otherwise the user won’t be able to see anything after login.
Save this setting and we would be navigated to login page.
Sign up with user “admin” and set a password and other details and log in using admin user.
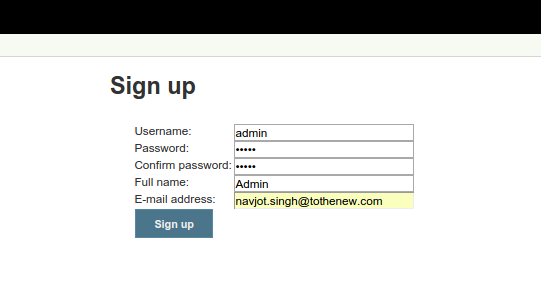
We can create “user1” the same way after logging out of admin.
Now, login in as admin user and create a job (say job1) and in configuration, select checkbox “Enable Project-based security” as shown below.
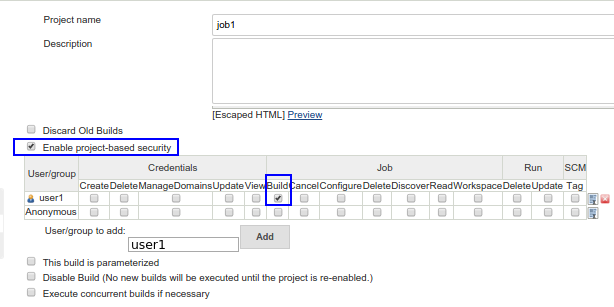
Add user “user1”, and give it “build” permissions under “Job” category and save the settings. This would enable “user1” to build this job when user1 would log in.
Alternatively, if we want user1 to have build permissions for every job which admin would create later on, we can select the “build” checkbox under “Job” category in “Configure Global Security.”
Since, we have provided all permission to “admin” while configuring global security, we do not need to add per project permission for admin.
With this, we can set global as well as per-project permissions for every user.
Can we hide a particular job for a particular project
actually after selecting “Project-based Matrix Authorization Strategy” i added only one user and then i clicked on save without checking the check boxes…..Now i am getting access denied when i am trying to login….if i create new account then also it is showing access denied….Please help me in this case how to reset the changes….thanks in advance
“We have to provide read permission under “Overall” category to any regular user otherwise the user won’t be able to see anything after login.”
Ran into the same issue and tried to disable security as suggested here:
wiki.jenkins-ci.org/display/JENKINS/Disable+security
this did not work for me so uninstalled and re-installed.