About OpenSSH
OpenSSH is an open-source suite of programs that helps us to secure network communications by encrypting the network traffic over many authentication methods and it provides secure tunneling. It eliminates eavesdropping, connection hijacking, and other such attacks.
Let’s learn Preventing Brute Force attacks due to OpenSSH Vulnerability (MaxAuthTries bypass).
Vulnerability
We have servers that use OpenSSH for authentication. Such servers can be exploited to carry out a brute force attack on OpenSSH protocol, making repetitive attempts to login with random passwords.
Anyone can exploit the vulnerability as the keyboard-interactive authentication is by default enabled on most of the systems.
Exploit code:
[js]ssh -lusername -oKbdInteractiveDevices=`perl -e ‘print "pam," x 10000’` targethost[/js]
![]()
Note:The exploit code only works with an automated script running in combination for password attempts.
This command will allow up to 10,000 password attempts provided that they are done within the login grace time (2 minutes by default) .
Attack Scenario
If an attacker requests 10,000 keyboard-interactive requests, OpenSSH will gracefully execute it inside a loop to accept passwords. In such scenario, the attacker will be able to do thousands of login attempts and they will be enough to achieve successful login by using a word-list of most commonly used passwords.
Version affected:
We can check the version of ssh on an ubuntu machine by the following command:
[js]ssh -V [/js]
![]()
This vulnerability is present in the latest version of OpenSSH i.e. 6.9.
Mitigating the attack:
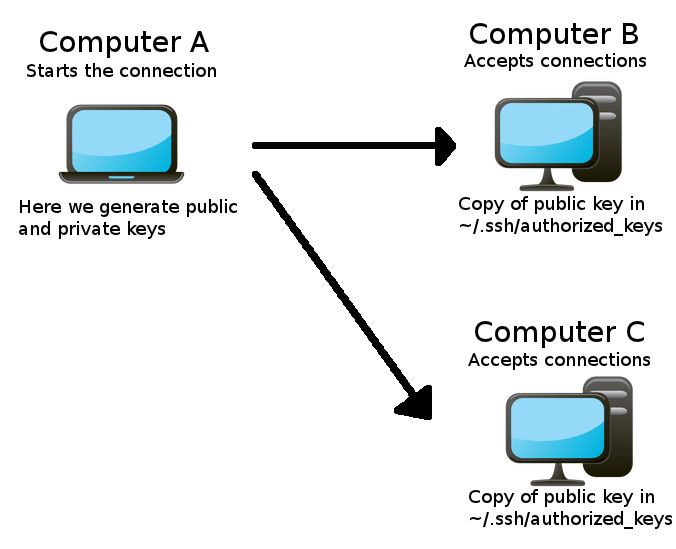
- Using a pem based (private key) authentication i.e. using a cryptographic key pair of at least 2,048 bits instead of password based authentication.
- Reducing the login grace period of OpenSSh to 20-30 seconds.
- Using Fail2Ban to limit the number of login attempts.
For detailed instructions about setting up Fail2Ban, you can go through this blog. - Upgrade to OpenSSH 7.0 as it is expected to be released in few weeks.
- Preventing brute force attacks via intrusion detection systems (IDS).
- Limiting ssh access only in the firewall.