Recently, I worked on a task wherein the users had to be authenticated based on existing Google credentials to get access of AWS Management Console. It took more time than expected to make it work as the documentation provided by Google is not complete. Let’s start by setting this up step by step.

Scenario:
Provide access of AWS Management console to already existing Google users. Let’s say the users belong to “singhnavjot.com” domain.
We will use SAML 2.0 protocol to pass information of Google user to Amazon’s AWS. Here, Google is our SAML Authority or Identity Provider and Amazon’s AWS is SAML consumer or Service Provider.
Let’s configure it to provide access to a user whose email id is “navjot@singhnavjot.com”.
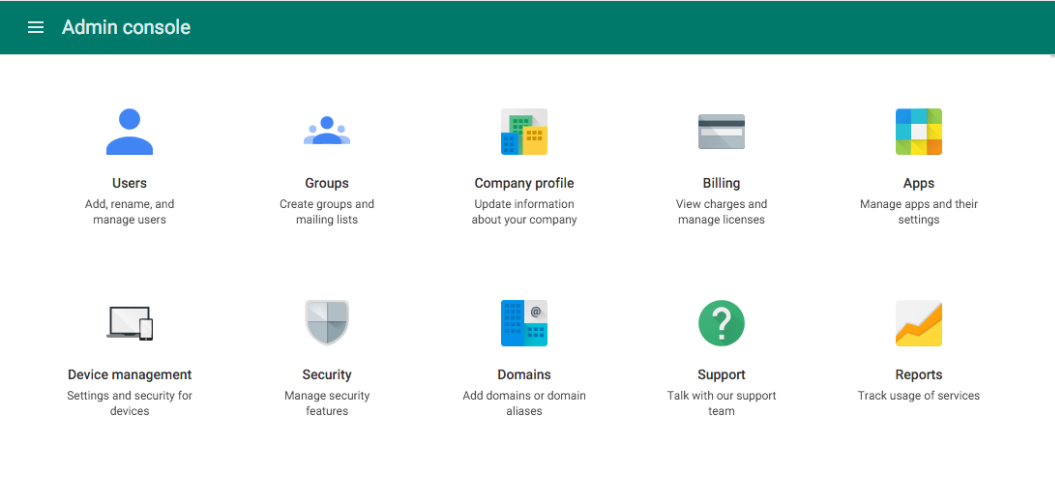
- Login into the Google’s admin console with the admin user. Once the below screen appears, click on “Apps”:
- Click on “SAML apps”:
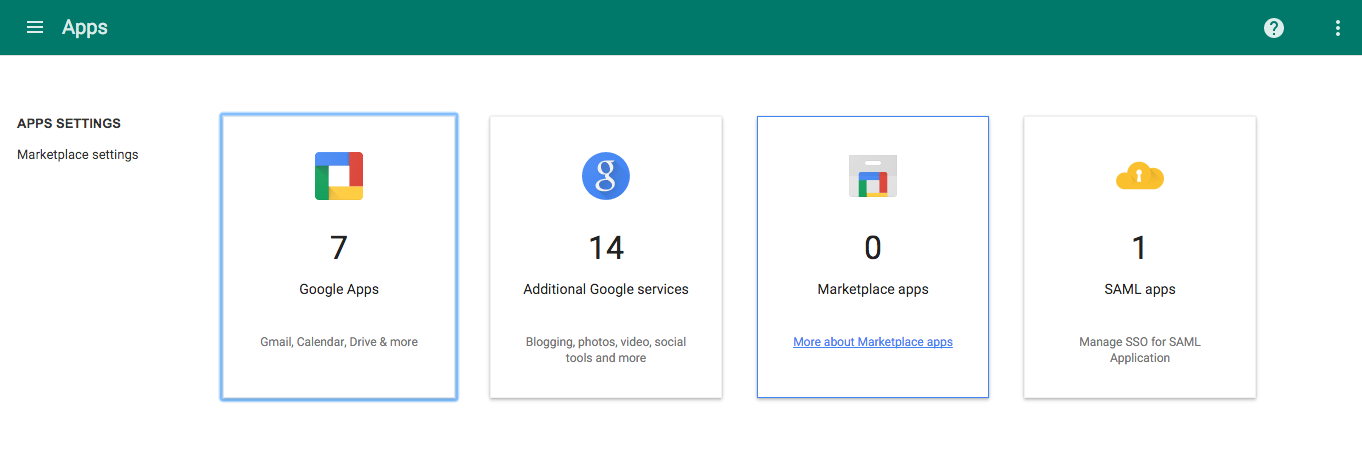
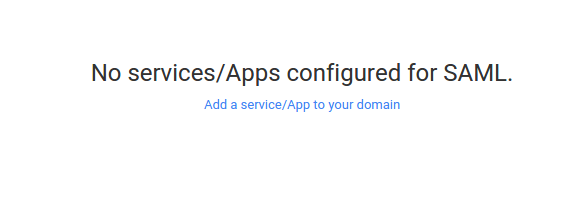
- Click on “Add a service/App to your domain”:
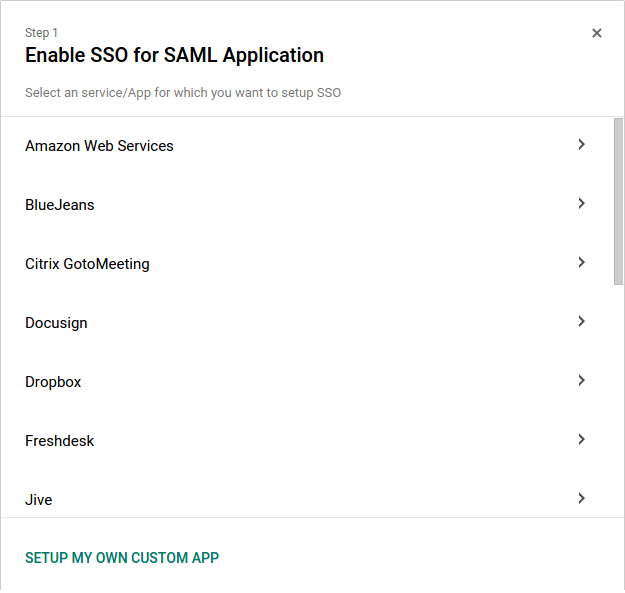
- Select “Amazon Web Services” from the list and click next:
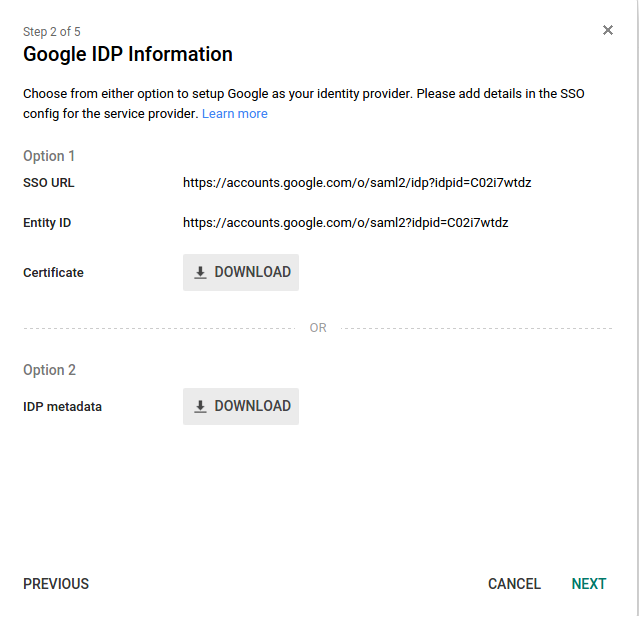
- Download the “IDP metadata” file. We need to upload this file in AWS console while creating Identity provider. Click next:
- AWS Management console’s settings: Login into AWS management console, go to IAM console and click “Identity Providers” present on the left pane:
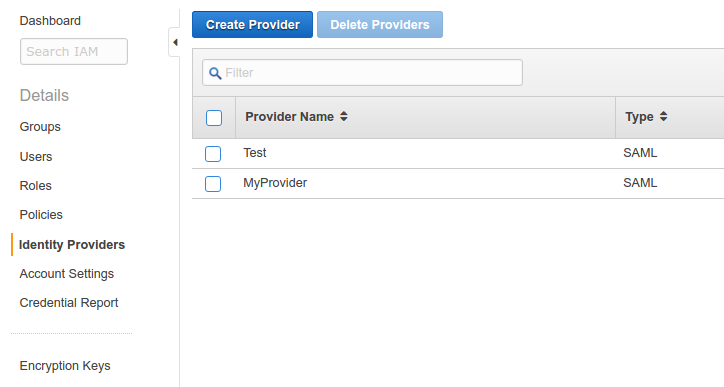
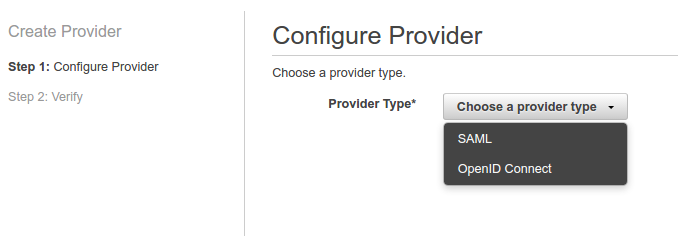
- Click on “Create Provider” and choose provider type as “SAML” from the drop down list:
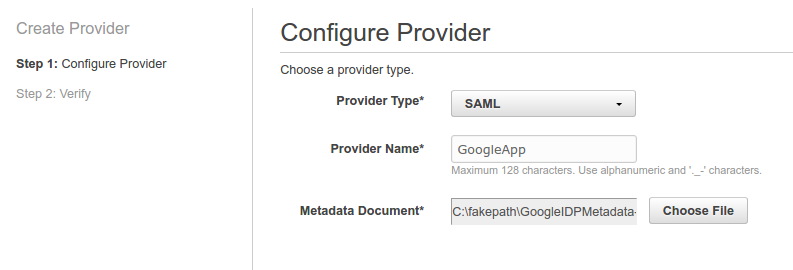
- Two fields will appear on the screen upon selecting “SAML”: “Provider Name” and “Metadata Document”:
Provide any name in the “Provider Name” field (say GoogleApp).
Upload the document downloaded in step 5 in the “Metadata Document”
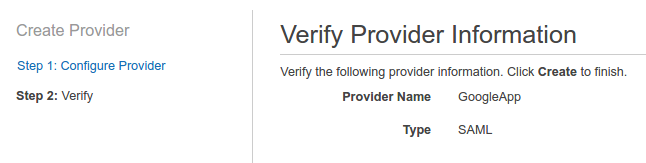
- Click “Next Step” present at the bottom right corner. Details verification page will appear. Save the “Provider ARN” as we will use it later. Save the Verify the information and click “Create” present at the bottom right corner:
- We have created the Identity provider successfully. Now, we need to a define access permission for this Identity provider. This can be done creating “Role” in AWS.
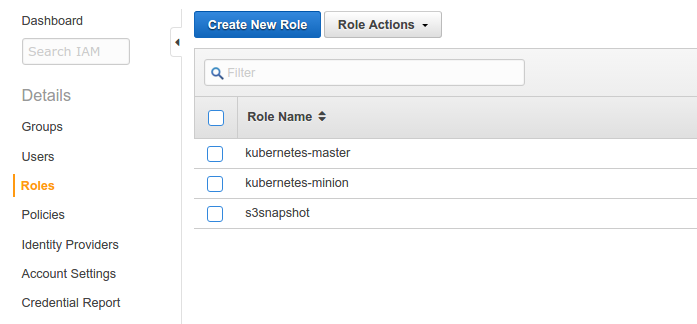
- Go to “Roles” in IAM console and click “Create Role”:
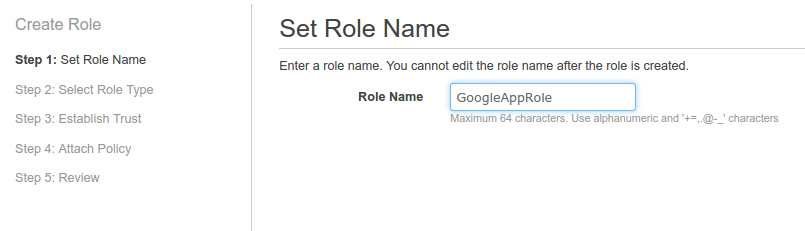
- Provide any name to the role (say GoogleAppRole) and click “Next Step” at the bottom right corner:
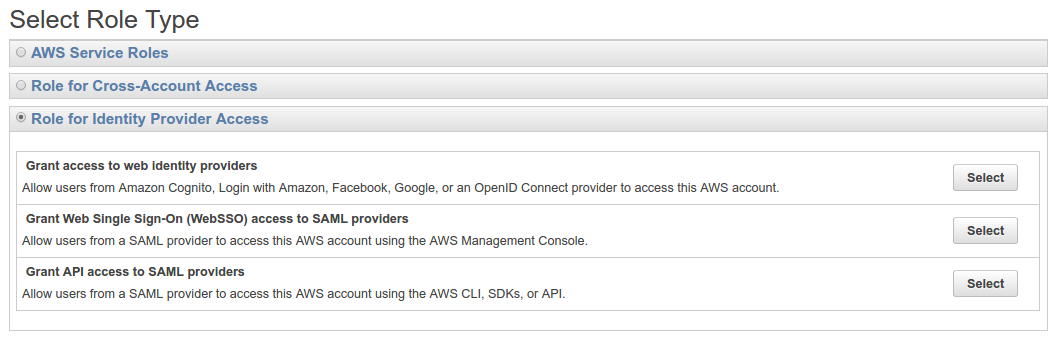
- Select “Role for Identity Provider Access” and then click “Select against “Grant Web Single Sign-On (WebSSO) access to SAML providers”:
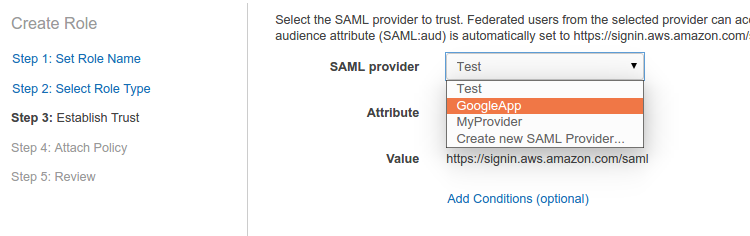
- Select “SAML Provider” which we have created in step 9 from the drop-down list and click “Next Step”:
- “Policy Document” will appear. Change it as per the requirement otherwise, this would work for us. Click “Next Step”.
- Select the policy from the list. We are selecting “ReadOnlyAccess” to provide our users who will use google credentials to login into AWS console a read-only access. Click “Next Step” to move to the verification page. Save the “Role ARN” as we will use it later.
- Click “Create Role” at the bottom right corner.
We have completed our AWS configuration. - We will now move back to the Google Admin Console which we have left in step 5 where we have downloaded the IDP metadata. Click next.
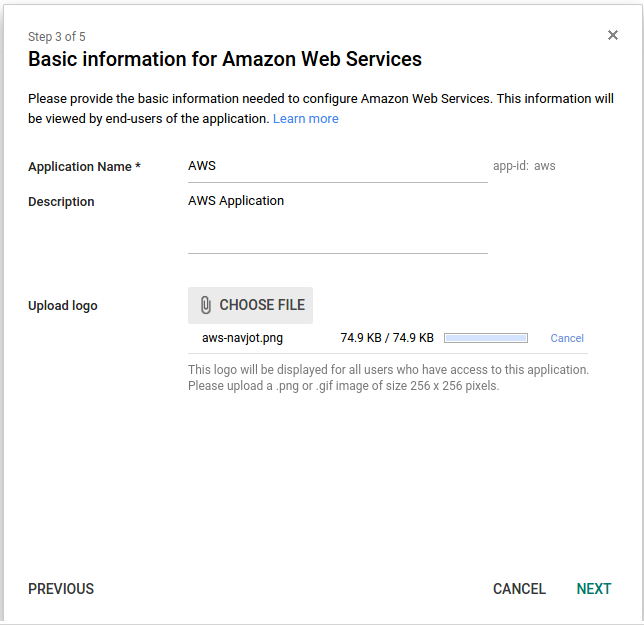
- Provide any name to your SAML application (say AWS) and any description in the description box. A logo can be uploaded. It is optional. Click next:
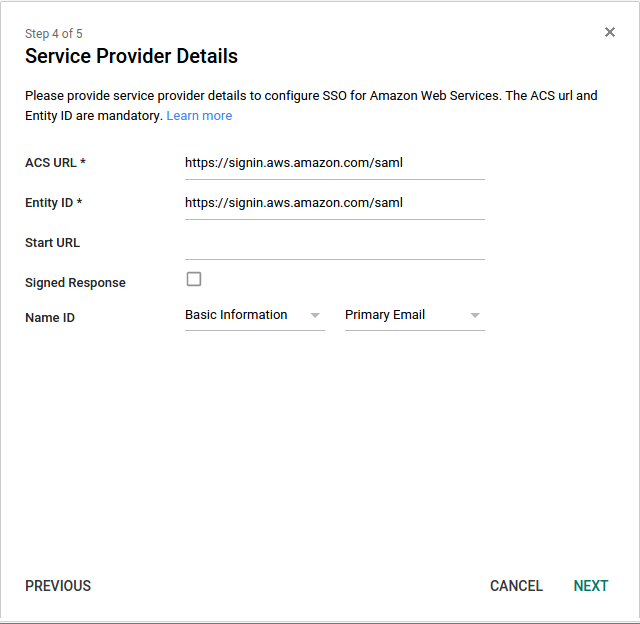
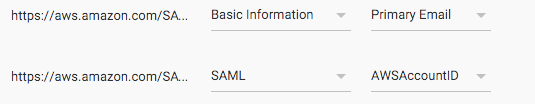
- Keep the ACS URL and Entity URL field intact. Keep the “Start URL” empty and “Signed Response” check box unchecked. In the “Name ID” field, select “Basic Information” and “Primary email” from the drop down list and click next:
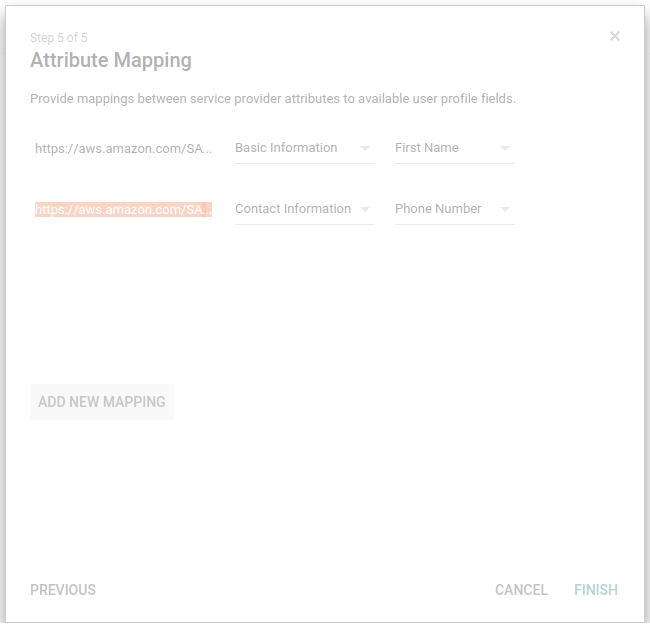
- In next step, we have two fields: “https://aws.amazon.com/SAML/Attributes/RoleSessionName” and “https://aws.amazon.com/SAML/Attributes/Role”. Choose anything against the fields present against them as we have to update it later. Click finish:
- We have not told google about the role and Identity provider ARN that it will use. For this, we need to add a custom field using google SDK API and API explorer in the Google App which would take Role and Identity Provider ARN. Google App will use these details to communicate with AWS.
- We will add one user into the app and provide it the access to use the AWS console using the provided AWS role.
- First we need to get the customer id using directory.users.get API.
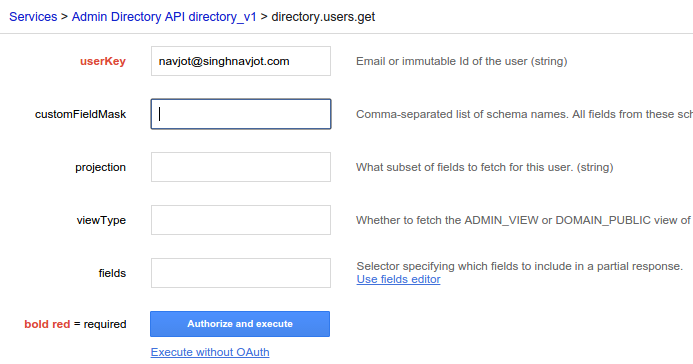
- Go to API explorer and click on the “directory.users.get” API in API explorer and fill your email id in the field “userKey” as shown below. Keep the other fields empty and click authorize and execute. Make sure we have admin permission:
- We will get 200 OK response with some information in the response. We can get “customerId” from the response.
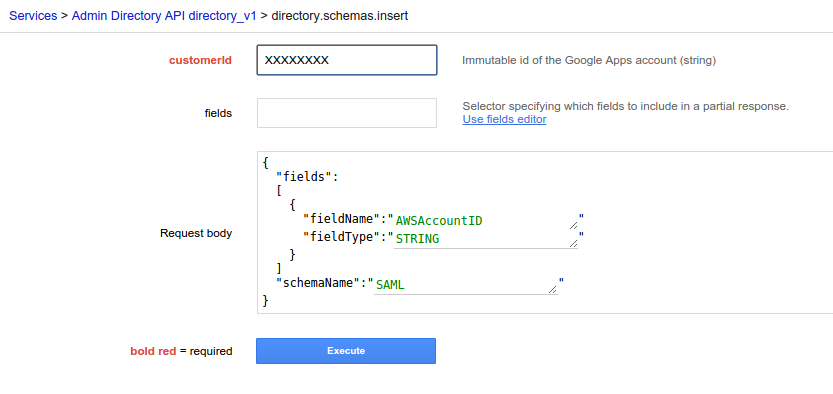
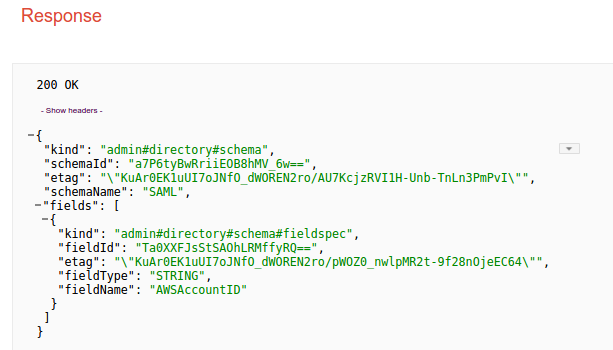
- Now, go to API “directory.schemas.insert and fill the customerId against the “customerId” field. Add the request body as shown below and hit execute and we will get 200 OK response. We have added a custom schema in our google app so that app can interpret the information that we will provide in the next step:
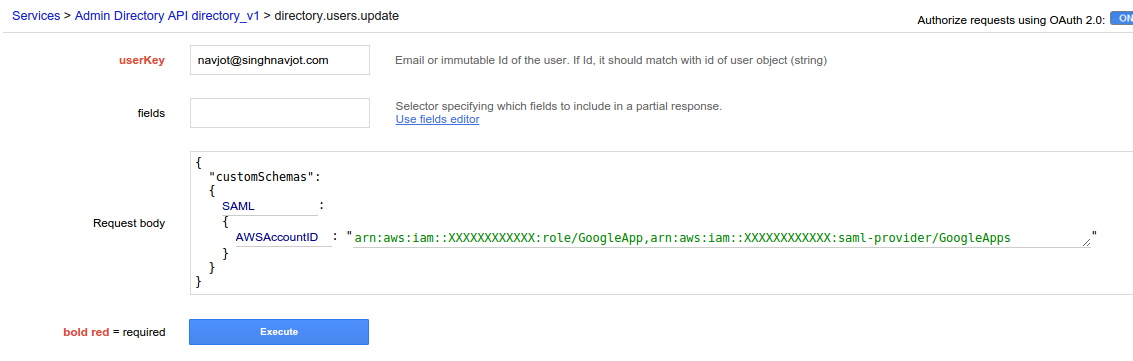
- Now, we are adding the AWS-related information in the fields using API directory.users.update.
- Go to the API and fill your email id again “userKey” filed and role ARN and identity provider ARN as shown below and hit execute which should return 200 OK response. We are adding user and specifying Provider and Role ARNs which we have saved while working on AWS console. So, for every user, we can use either same or different Provider and Role ARN. The ARN specified below are comma separated:
- Now, we have added new custom schema and populated the fields. If we have only a few users then these steps can be repeated for all users.
- Now, go back to the google samSAMLl app and edit attribute mapping as follows and hit save:
- Now, we need to enable this app for users as follows:
- That’s all we need to do configure in the Google admin console.
- We can launch the app from the highlighted icons present at the top right side of the screen:
Upon launching the App we will be redirected to the AWS management console having ReadOnlyAccess. Similarly, different access permission can to granted to different users by assigning separate to the users.
How i can configure more than 10 aws accounts to each google user?
On step 29, you can add as my accounts and roles as you want per user by adding:
,{
“value”: “arn:aws:iam::RootAccountNumber:role/gAwsRole,rn:aws:iam::RootAccountNumber:saml-provider/ProviderName”,
“customType”: “RoleDescription”
}
Have you used SAML to generate temporary tokens for use with the AWS CLI?