Upgrading the Terraform AWS Provider: Painful, But Worth It
Introduction
If you’re using Terraform for IAAC with AWS, you might have probably declared the provider like this in your code:
provider "aws" {
region = "us-west-2"
}

terraform + aws
And it worked. So you left it alone. Then one day, someone tries to use a newer module… and Terraform throws a special error:
Error: unsupported argument
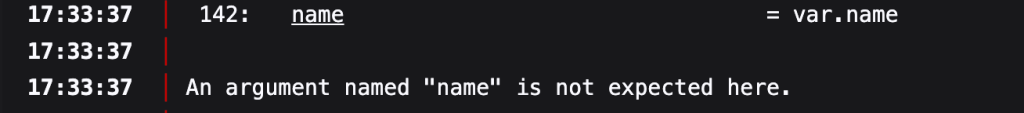
unsupported_argument
This version of the AWS provider does not support…Boom. Welcome to the wild world of Terraform AWS provider upgrades.
We recently upgraded the AWS provider from version 4.X.X to 5.X.X for one of our ad-tech clients. The upgrade impacted over 20 Terraform modules and dozens of AWS resources – from ALBs to IAM roles. In this blog, let’s break down:
- Why is upgrading the AWS provider so painful?
- What do you gain by doing it?
- A practical way to approach upgrades with less fear
Why It Hurts So Much
Let’s be honest: upgrading the AWS provider isn’t always fun. These are the main reasons:
1. Making Breaking Changes
- Breaking changes are introduced by the AWS provider every few versions:
- The names of resource arguments (lifecycle keys, timeouts, etc.) change.
- Changes in output structure
- Some deprecated resources are also eliminated.
After the upgrade, your functional infrastructure code might all of a sudden stop applying or planning.
2. Incompatible Modules
Version discrepancies can ruin everything if you’re using Terraform modules, whether they’re yours or ones from the open registry:
- Newer provider features might not be supported by older modules.
- You might not be on the provider versions needed for newer modules.
You’re now caught between:
- “I require the new features of the module.”
- “However, my provider version is unable to manage them.”
3. Terraform Core Dependencies
Sometimes, the provider version also needs a newer Terraform CLI — say, >= 1.1. Then you’re dealing with more than just one upgrade. You’ve got CLI behavior changes, reinitializations, and state concerns, too.
What You Gain
Now for the good news: the pain is temporary — the benefits are long-term.
1. Support for New AWS Features
AWS keeps launching new features — and the only way to use them in Terraform is to upgrade the provider.
Example:
- VPC Lattice, AWS Elasticache Valkey, CloudWatch Metric Streams, IAM Roles Anywhere — all needed recent provider versions to work.
- Want to use PrivateLink with supported services? New provider only.
2. Bug Fixes and More Stable Behavior
Terraform AWS provider gets frequent bug fixes:
- Stale state issues
- Inconsistent diffs
- Timeout problems
- All patched quietly in newer versions.
- We once had a Terraform plan that showed a diff every time for S3, even when nothing changed.
- Upgrade fixed it.
3. Cleaner, More Predictable Code
Newer providers often clean up the resource schema, reduce duplication, and support better for_each, dynamic blocks, and lifecycle features. Your code gets more powerful, reusable, and clean.
How We Do the Upgrade (Without Losing Our Minds)
Here’s a process we’ve developed after a few painful attempts:
Step 1: Upgrade in a Sandbox First
Spin up a fresh repo/environment and test the new version there first.
Update your versions.tf like:
terraform {
required_providers {
aws = {
source = "hashicorp/aws"
version = "~> 5.100.0" # your new version
}
}
}
Then do a:
-
terraform init -upgrade
-
terraform plan
Watch what blows up.
Step 2: Read the Changelog (Seriously)
HashiCorp maintains changelogs for the AWS provider.
Look for:
- Deprecated arguments
- Changed defaults (timeouts, SSL enforcement)
- Required Terraform core version
- Yes, it’s boring. Yes, it saves hours of debugging.
Step 3: Upgrade One Environment at a Time
If you have dev → qa → integration → preprod → prod environments, upgrade dev first. Let it run for a few days. Watch for:
- Module incompatibility
- Resource recreation risks
- Unwanted changes in diff
- Once confident, move to staging, then prod.
Step 4: Update All Team References
Update provider version in:
- Shared modules
- CI/CD pipelines
- terraform-docs, tfsec, or other tooling
- Avoid the split-brain of half your repos running old versions.
Step 5: Lock It with required_providers
Always pin your provider version to avoid accidental upgrades during CI/CD or terraform init:
terraform {
required_providers {
aws = {
source = "hashicorp/aws"
version = "~> 5.100.0"
}
}
}
Bonus Tip: Track Provider Versions Across Projects.
Use a simple script or tool to scan your Terraform codebases. Identify where provider versions are outdated or mismatched. This keeps everyone aligned.
Final Thoughts: The Cost of Delay
The longer you delay a provider upgrade:
- The bigger the version gap
- The harder it gets to resolve
- The scarier your diffs become
We’ve learned that small, regular upgrades (every 2–3 months) are way better than one massive leap every year.
At TO THE NEW, we specialize in solving real-world DevOps challenges, from state management to large-scale infrastructure transformations on AWS, Azure, GCP, and other cloud providers. Whether you’re modernizing Terraform practices or planning a zero-downtime migration, our certified AWS architects and DevOps engineers are here to ensure your cloud journey is efficient, reliable, and future-proof. Terraform is about predictable infrastructure — don’t let an outdated provider throw chaos into the mix.
Stay connected for more practical insights as we continue to simplify cloud operations and enable smarter infrastructure decisions.



