This blog post refers to a use case I came across recently wherein, a few users had to remotely log into the server using SFTP. These users should be restricted to perform read/write operation only in their home directory and only from office network i.e the public IP address(es), their office network is fabricated upon. To achieve this, we have to create SFTP users on Linux machine and those users should have only read/write privileges only in their home directory and access should be allowed only from a particular public IP (lets say public IP of their office network). This blog assumes SSH service is already running on the Linux machine and below commands has been tested on ubuntu 14.04
Steps to create restricted SFTP users,
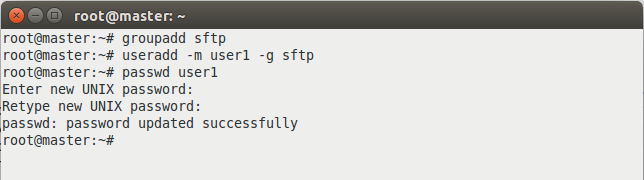
1) Create a user group
[js]groupadd sftp[/js]
2) Create users in above group and set the password,
[js]useradd -m user1 -g sftp[/js]
[js]passwd user1[/js]
3) Edit /etc/sshd/sshd_config
3.a) Enable password authentication so that users can login using their respective passwords.
[js]PasswordAuthentication yes[/js]
3.b) Only users included in sftp group should be able to perform sftp login
[js]Match Group sftp[/js]
3.c) Mention users along with their network’s public/real IP addresses (Public/real IP address can be obtained by running command #curl ifconfig.me
[js]AllowUsers user1@<public ipaddress1> user2@<public ipaddress1> user2@<public ip address2>[/js]
3.d) Restart the ssh service
[js]service ssh restart[/js]
4) After successfully completing above step, check if the implementation has taken place successfully by trying to sftp login with the above created user. To log into server, you must have IP address of the server,
[js]sftp user1@<server public ipaddress>[/js]
If above user login command executed successfully, it will login intelligrape with sftp shell prompt.
Regards
Sharad Aggarwal